This post covers the configurations and the required steps to achieve Oracle Access Manager Password Management Use-cases. In this set-up there is no integration with Oracle Identity Manager. In this set-up Oracle Access Manger version is 11gR2 (11.1.1.2) and OUD acts identity store.
Below are the main use-cases will be addresses using this password management.
- Manage password policy the rules (ex: Minimum length, Special characters, Max no of attempts etc.)
- Force the user to modify the password on first login
- Force the user to modify the password if it is expired
- Notify the user when the password will expire
- Force the user to modify the password if it does not meet the password policy (from LDAP)
- Lock user based on the failed login-attempts; unlock the user based on the configurable time
Prerequisites
Before proceed with the below steps, make you have below environment/configuration already in place
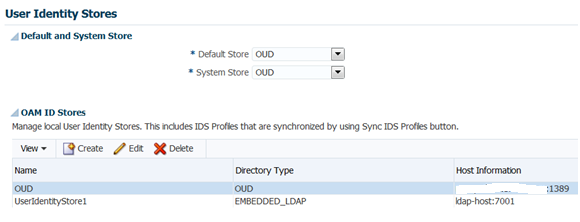
- OAM environment installed and configured with OUD as default & system store
- Webagte is registered and also has integration with OHS .
- Make sure index.html from the OHS is protected with OAM and able to access the same after providing the user information from OUD
Configurations
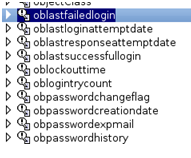
Extend LDAP Schema
1. Extend LDAP (OUD) schema with the OAM related objectclasses and the attributes.this is store the user password information.
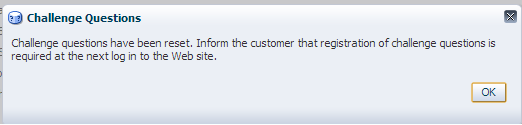
Go to this locatiom Location – <Oracle_HOME>/oam/server/pswdservice/ldif
ex:cd /u01/app/oracle/product/middleware/Oracle_IDM1/oam/server/pswdservice/ldif/
2. Identify the required LDIF file and execute the following command (the command parameters may change based on your environment/ldap)
ex: cd /u01/app/oracle/product/middleware/asinst_1/OUD/bin
./ldapmodify -h <hostname> -p 1389 -D cn=”Directory Manager” -f u01/app/oracle/product/middleware/Oracle_IDM1/oam/server/pswdservice/ldif/OUD_PWDPersonScheme.ldif
3. After successful execution of the command verify the weather schema is extended with the objectclass and the attributes mentioned in the LDIF file
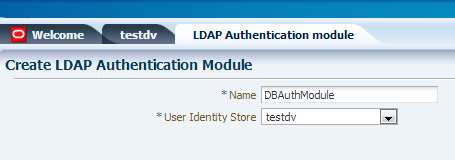
Configure Authentication Modules
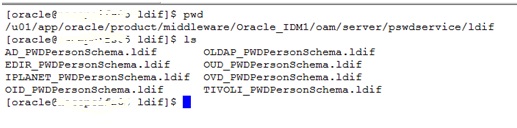
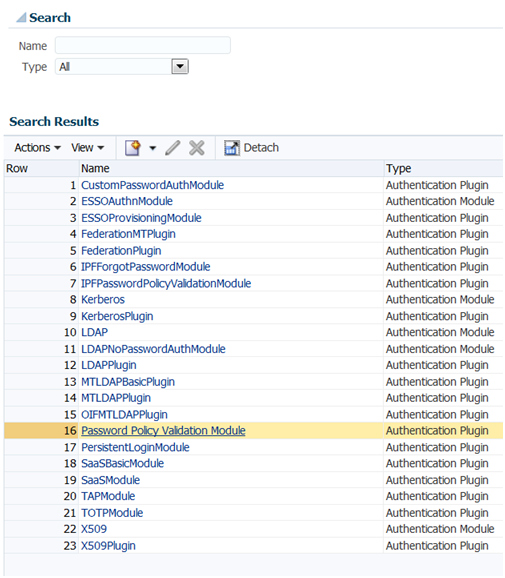
- Login to Oracle Access Manager Admin Console
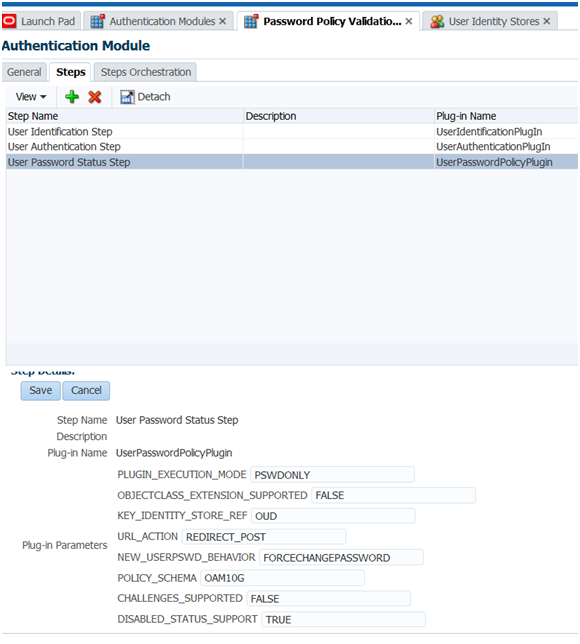
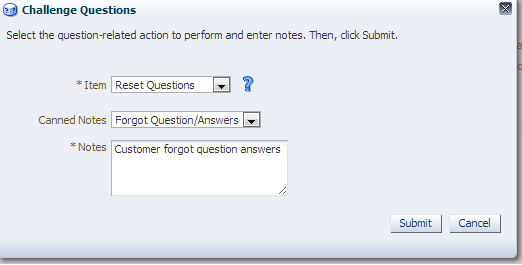
- Got o Authentication Modules->Select Password Policy Validation Module
 3. Go to the Steps Tab Select User Identification Step and provide the Plug-in Parameters as shown below (Values may change based on your environment).
3. Go to the Steps Tab Select User Identification Step and provide the Plug-in Parameters as shown below (Values may change based on your environment).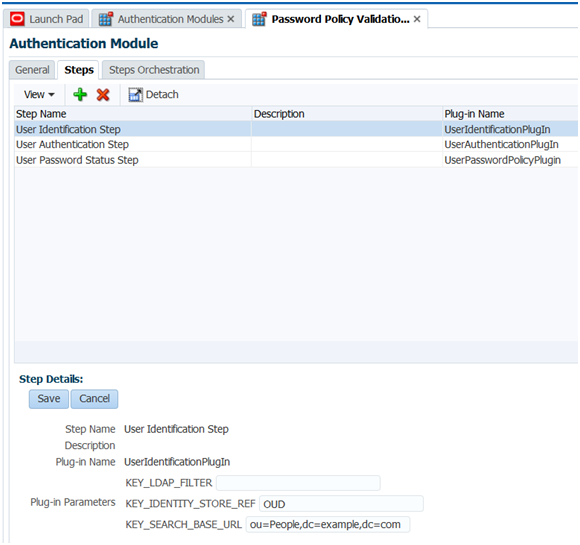
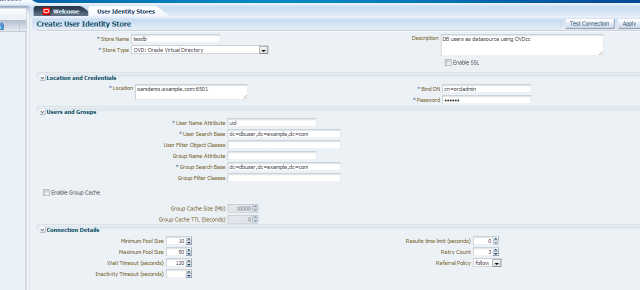
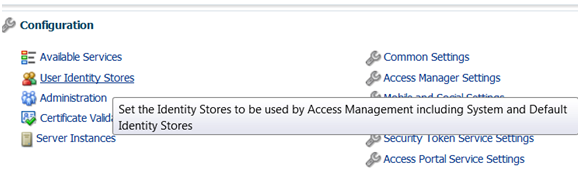
- To identify KEY_IDENTITY_STORE_REF go to the LaunchPad->Configuration->User Identity Stores, in this case the value is OUD
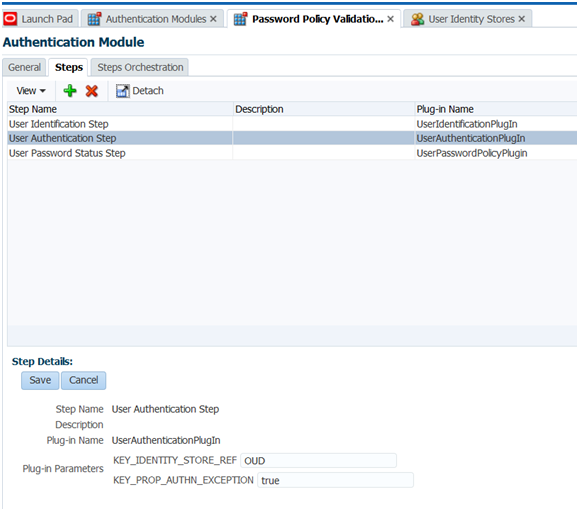
- Select the User Authentication Step and provide the values as shown below
 5. Select User Password Status Step and provide the values as shown belowMake sure NEW_USERPSWD_BEHAVIOR to FORCECHANGEPASSWORD
5. Select User Password Status Step and provide the values as shown belowMake sure NEW_USERPSWD_BEHAVIOR to FORCECHANGEPASSWORD
6. Make sure click on Save for all the steps and click on Apply
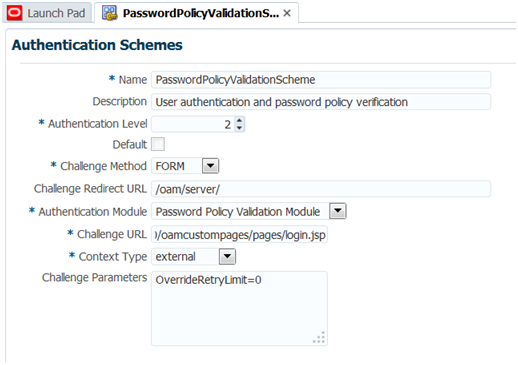
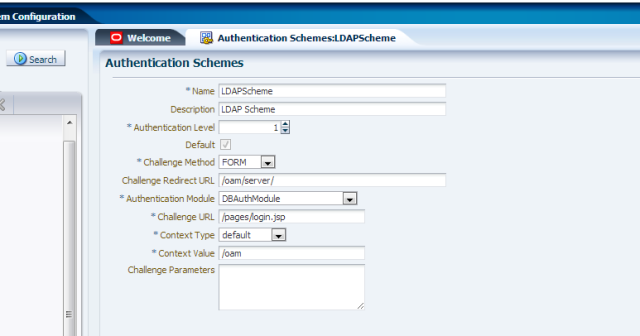
Configure Authentication Schemes
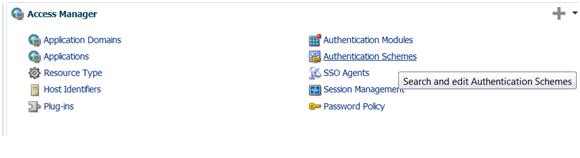
- Go to the Authentication schemes->Click on search->Password Policy Validation Scheme
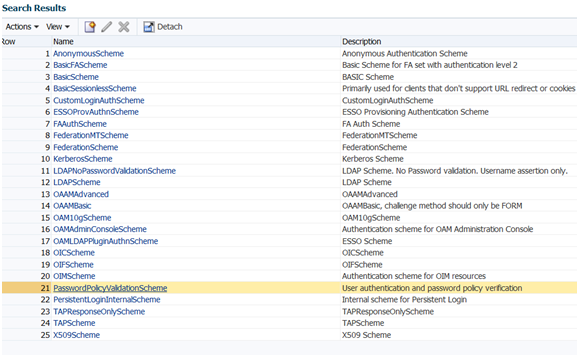
2. Provide the values as shown below and the challenge url will be http://<hostname> :14100/oamcusompages/pages/login.jsp( this page is from the war file we are going to deploy on OAM Server in the next steps)
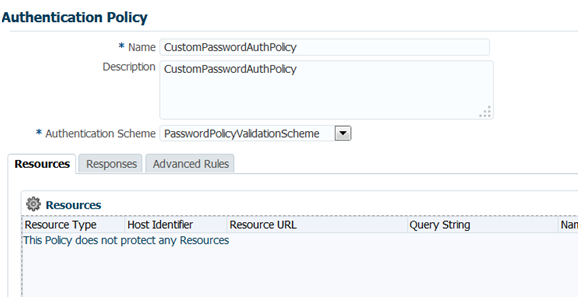
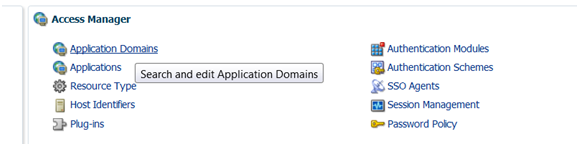
Configure Application Domains
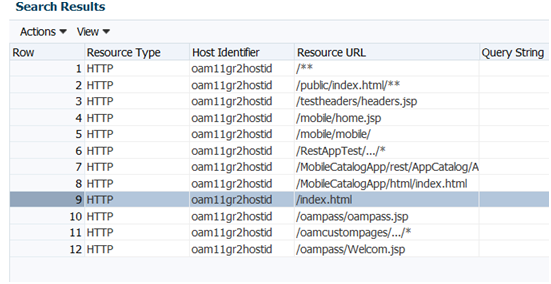
- Go to the Application Domains->Webagte->Resources
 2. Make you have index.html in the resource if not add the same
2. Make you have index.html in the resource if not add the same
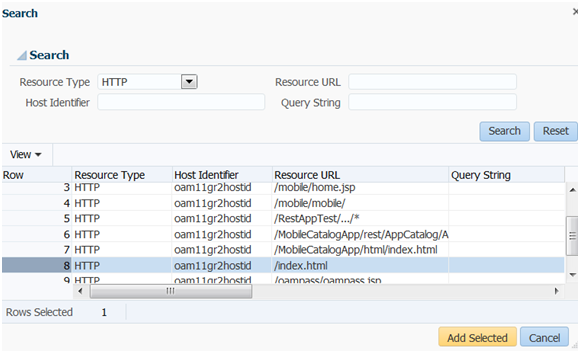
 3. Click on the Authentication policy tab->Create Authentication Policy and create the policy with the below parameters
3. Click on the Authentication policy tab->Create Authentication Policy and create the policy with the below parameters
4. Click on the + symbol to add the resource index.html and click on Apply
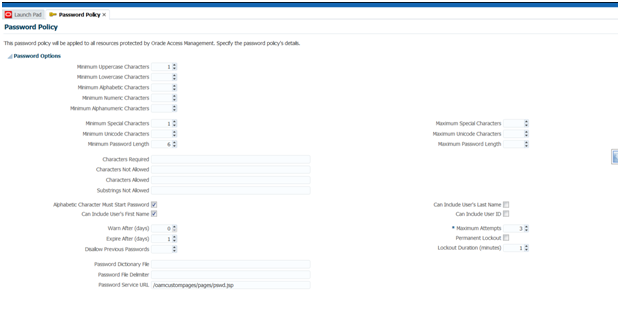
Password Policy
- Go to the launch pad->Access Manager->Password Policy
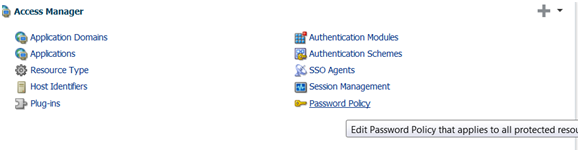 2. Verify the parameters and set Password Service URL as /oamcustompages/pages/pswd.jsp(we are going to deploy this pages in the next steps)
2. Verify the parameters and set Password Service URL as /oamcustompages/pages/pswd.jsp(we are going to deploy this pages in the next steps)
Deploying the OAM Custom Password Application
The are some issues with the war file comes with the product installation. If you would like see what are the issues and the fixes go through the below steps.
Refer the Oracle support site for more information on this.
- Get the oamcustompages.war from the below location. <Middleware_Home>/Oracle_IDM1/oam/server/tools/custompages
- Extract the war file to temporary location
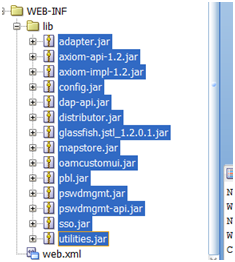
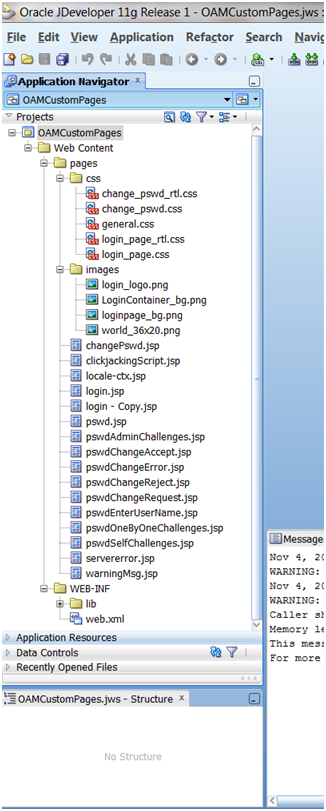
- Create new project using Jdeveloper and add the JSP’s,css,images and other files as shown below
 4. Get the oam-server.ear from <middleware_Home>/Oracle_IDM1/oam/server/apps
4. Get the oam-server.ear from <middleware_Home>/Oracle_IDM1/oam/server/apps
5. Extract the same to the temp location and add the below lib files from the same
6. Get the gasllfish_jstl_1.2.01.jar from \oam-server\ngsso-web\WEB-INF\lib
7. Create clickjackingScript.jsp file /pages with below content<%@page session=”false”%><style id=”antiClickjack”>body { display: none !important; }</style><script type=”text/javascript”>
if (self === top) {
var antiClickjack = document.getElementById(“antiClickjack”);
antiClickjack.parentNode.removeChild(antiClickjack);
} else {
top.location = self.location;
}
</script>
Update below files to refer clickjackingScript.jsp properly
changePswd.jsp
pswdAdminChallenges.jsp
pswdChangeAccept.jsp
pswdEnterUserName.jsp
pswdOneByOneChallenges.jsp
pswdSelfChallenges.jsp
warningMsg.jsp
8.In each of the above files,Replace<!– Start Disable frame hijacking Script–><%java.net.URL srcURL = new
java.net.URL(request.getRequestURL().toString());
String reqURL = srcURL.getProtocol() + “://” + srcURL.getHost() + “:”
+ srcURL.getPort();
%>
<c:set var=”hostUrl” value=”<%=reqURL%>” />
<c:import var=”antiClickJackingScript”
url=”${hostUrl}/oam/pages/clickjackingScript.jsp” charEncoding=”UTF-8″ />
<c:out value=”${antiClickJackingScript}” escapeXml=”false” />
<!– End Disable frame hijacking Script–>
With
<!– Start Disable frame hijacking Script–>
<%@ include file=”/pages/clickjackingScript.jsp” %>
<!– End Disable frame hijacking Script–>
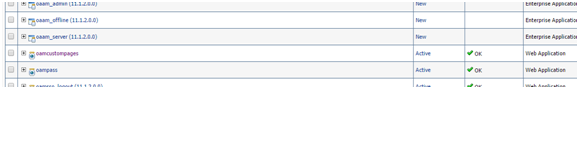
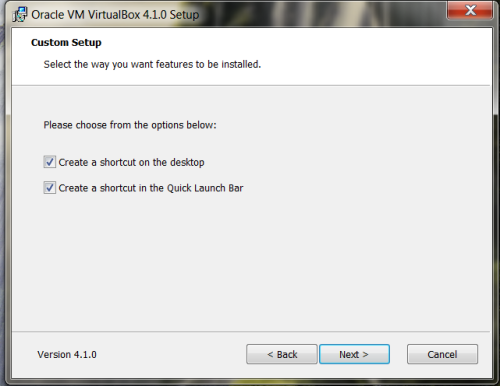
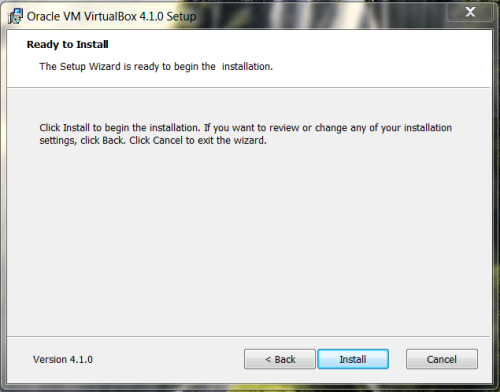
9. Now deploy the war file to your weblog OAM Server and make sure the status is Active
Use Cases
Force user to change their password the first time they log in
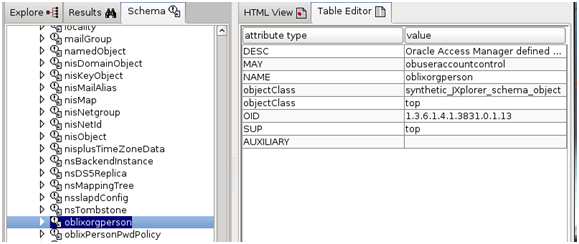
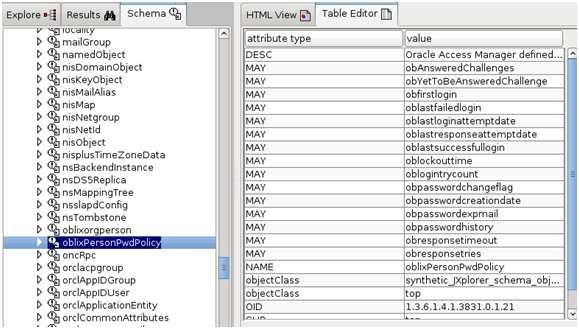
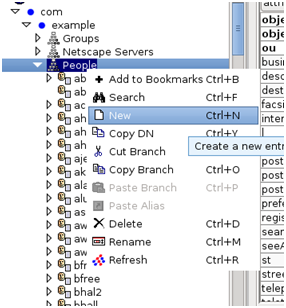
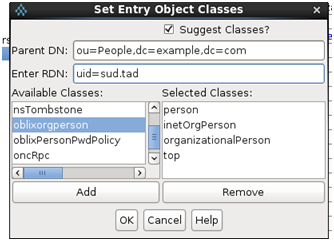
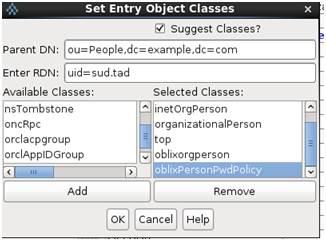
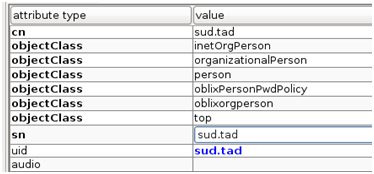
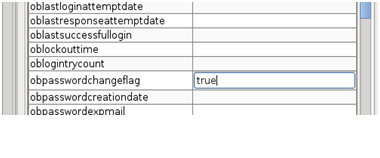
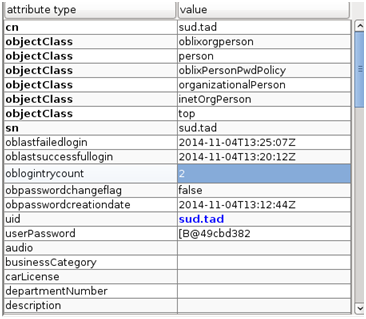
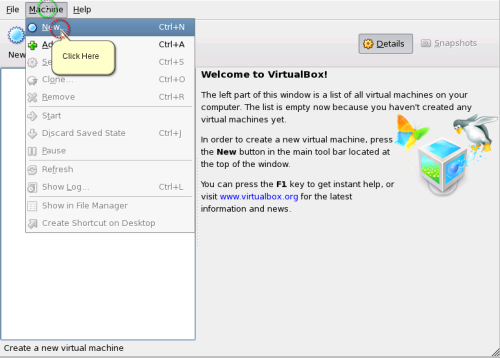
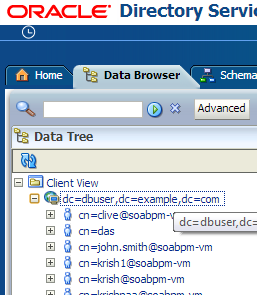
- Create new user in OUD and assign the oblixorgperson and oblixPersonPwdPolicy object classes as shown below.
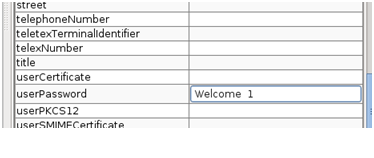
- Assign the other mandatory fields and set the password as Welcome_1(in this case)
- Also assign obpasswordchangeflg to true
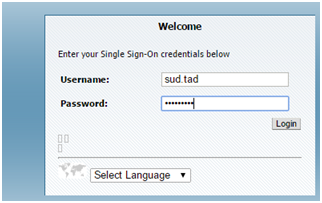
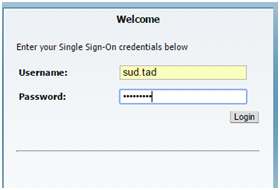
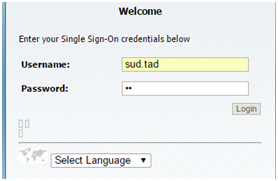
4. Now access the protected resource i.e http://<hostname>:7777/index.html and see OAM redirects to the login page.
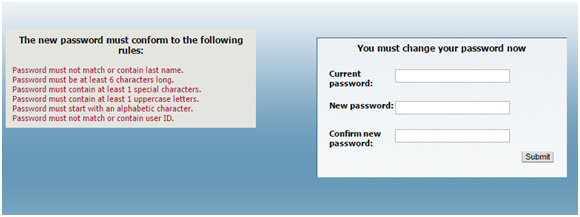
5. Enter the credentials of the user and see the OAM password management validates the policies and re-direct the user to password change page
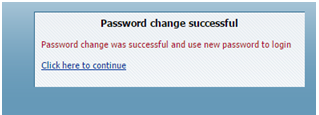
6. Observe the password policy rules and enter the old password and new password and verify the success page and click on continue.
Password Expiry Notification
- Login to Oracle Access Manager Console-> Launch pad->access Manager->Password Policy
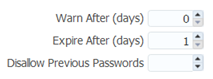
- And set the below values for demo purpose and click on apply
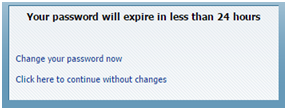
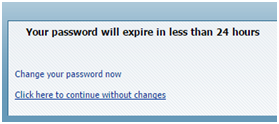
3. Now access the protected resource with the new password provided in the previous step.
4. Observe the notification for the password expiry.’
5. Choose the option you would like to proceed
Account Lock & Unlock
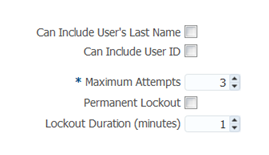
- Go to the password policy and provide the values as shown below
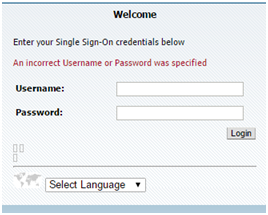
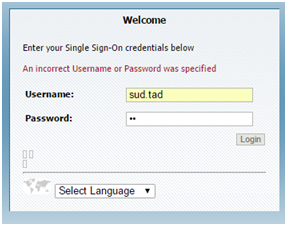
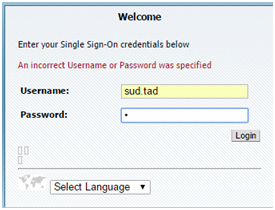
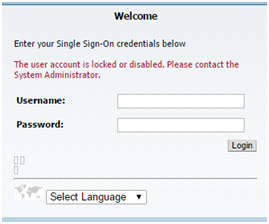
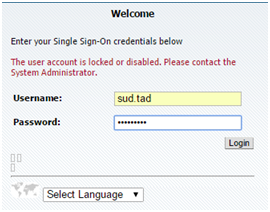
2. Now access the protected resource with wrong password for 3 times and see the message
3. You can verify the value in the LDAP
4. Wait for 1 min for the lockout and see whether you are able to login again
This concludes the configurations & the use-cases